2024极客大挑战 复现
2024极客大挑战
RE
cpp_flower
思路
知识点
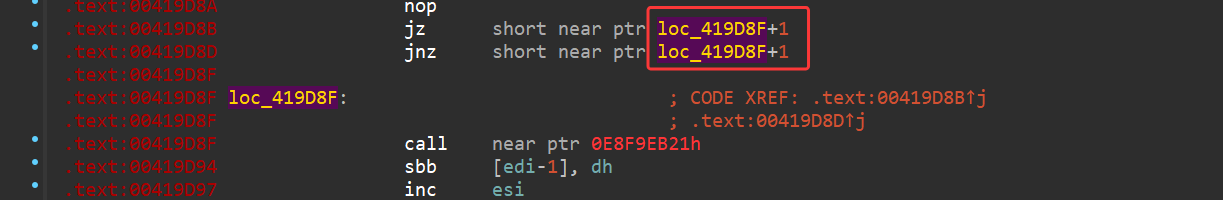
这题就是一个纯花指令,主要有两个部分的花指令特征:
jnz/jz addr+1
就像下面这种:
patch方法可以直接将第一个jz改成jmp,再重新分析成代码:
- 第二种就是call一个函数,然后修改ret_addr:
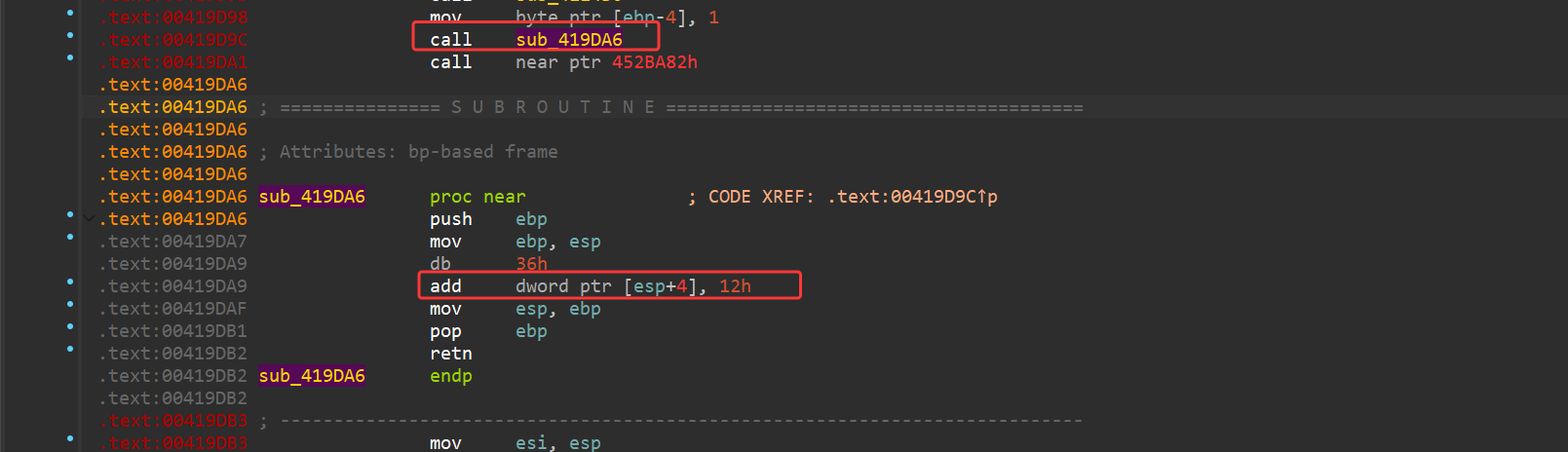
就像这种,这里大致功能就是jmp到0x419db3。
patch方法就是直接改成jmp到指定位置即可。
修复完成后逻辑如下:
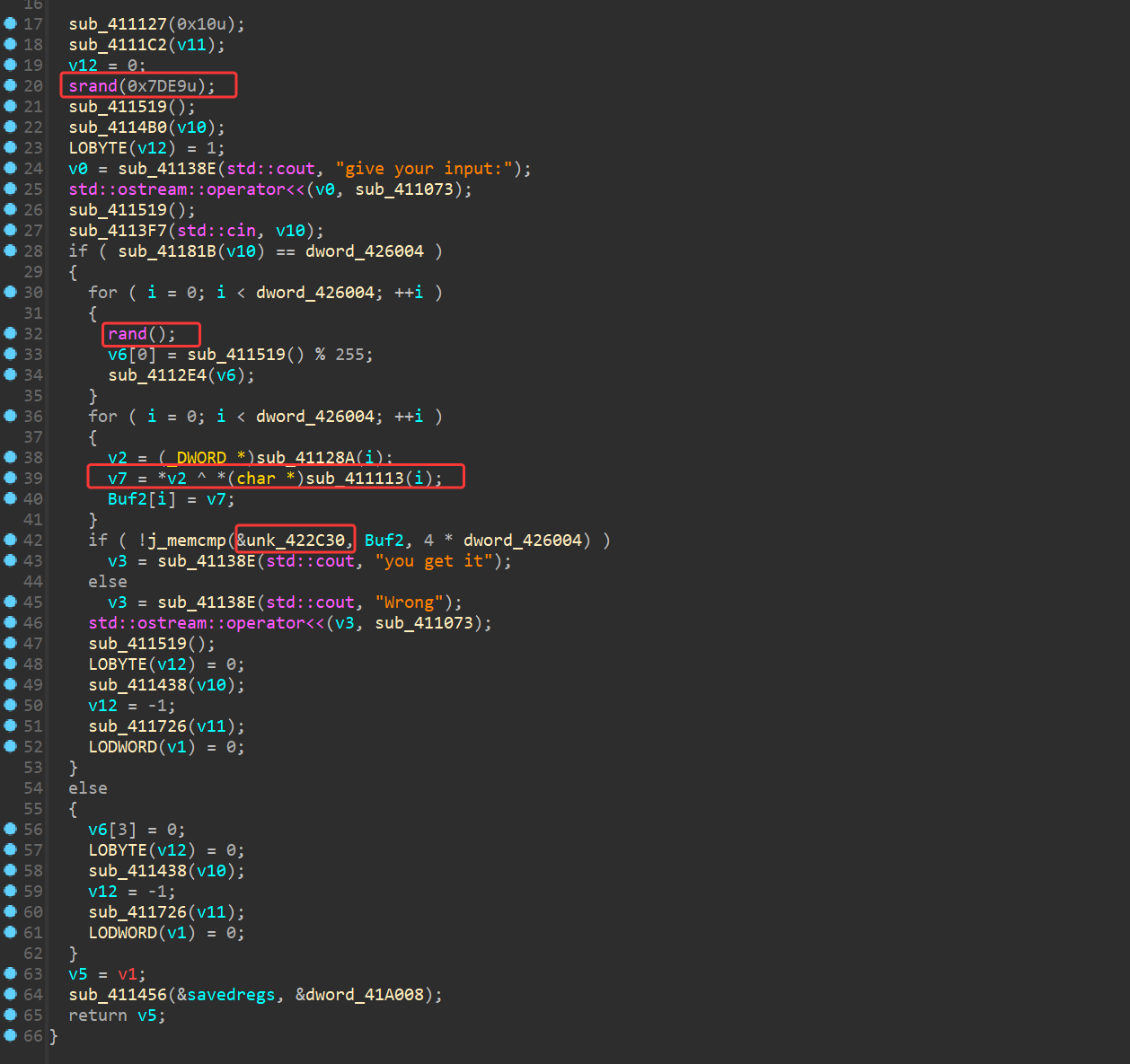
大致意思就是先srand(0x7de9),然后每个随机数模255和input异或,最后和unk_422c30比较。
EXP
1 | void cpp_flower() |
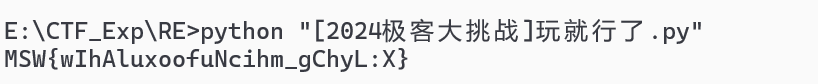
玩就行了
思路
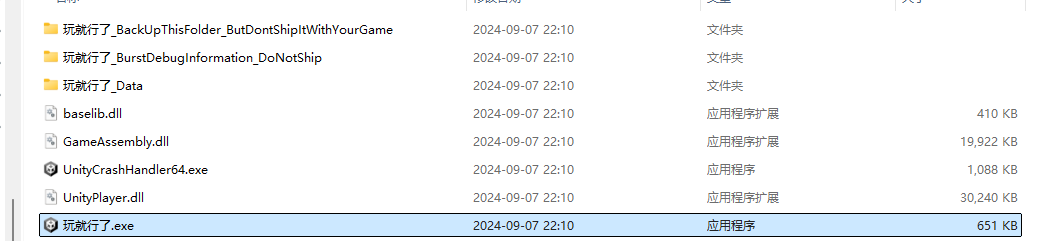
附件是一个Unity的游戏,先看看根目录有啥:
启动游戏:
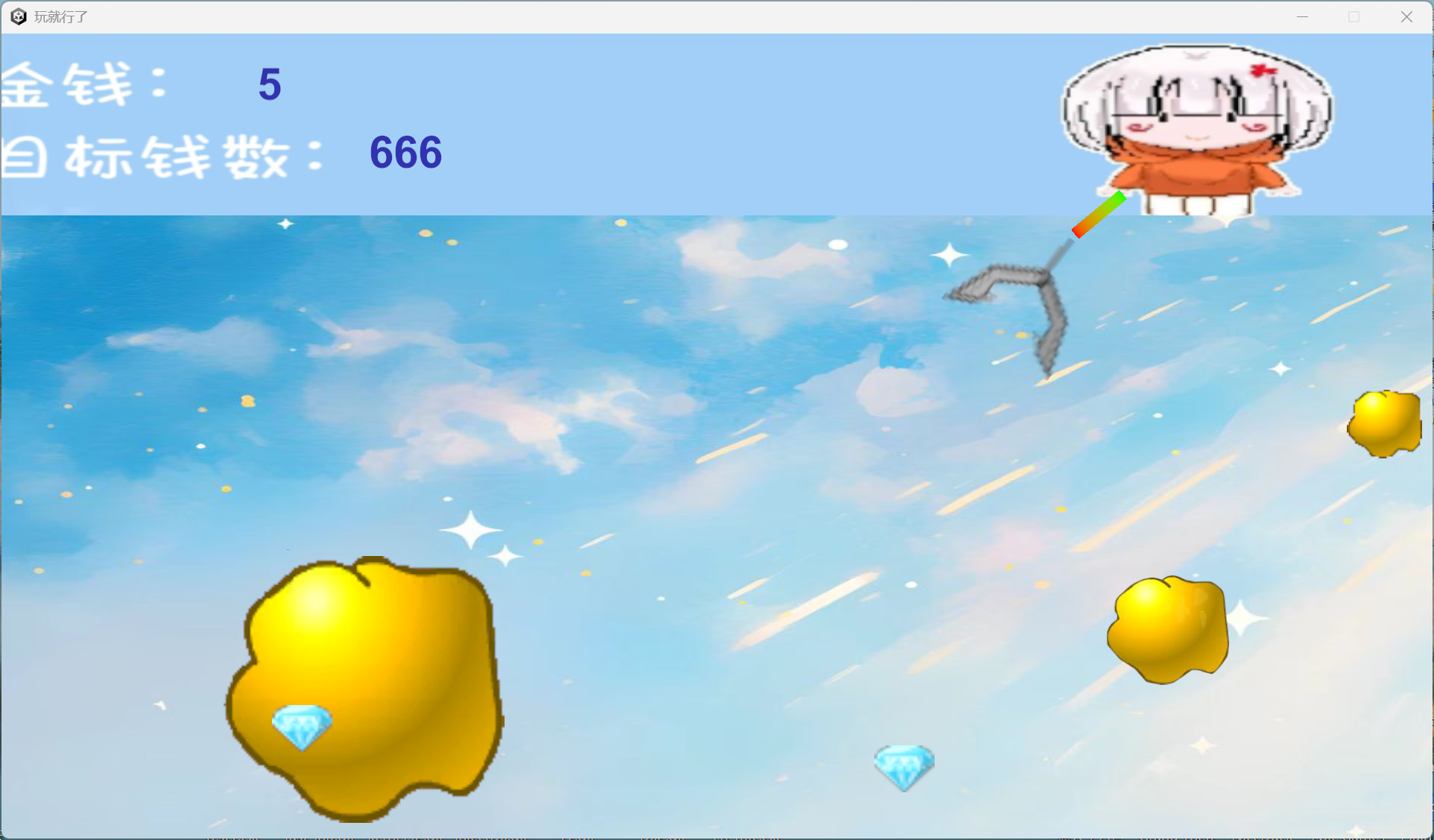
有个金钱数,直接CE改一下数值比较方便,改完后出了提示:

再看看根目录有啥:
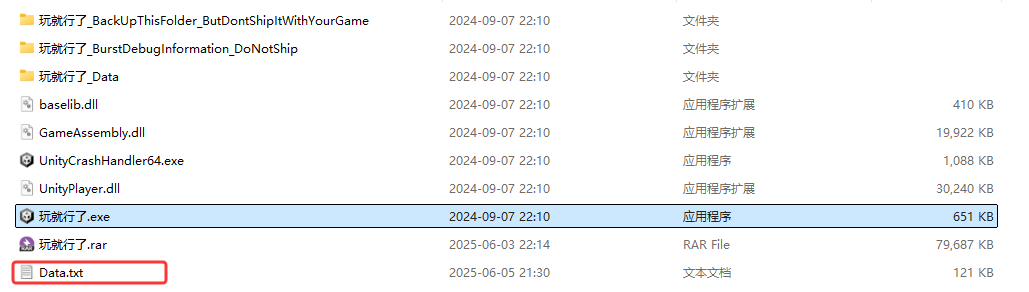
多了个data,看看什么东西,发现开头4d5a,写个脚本转二进制文件:
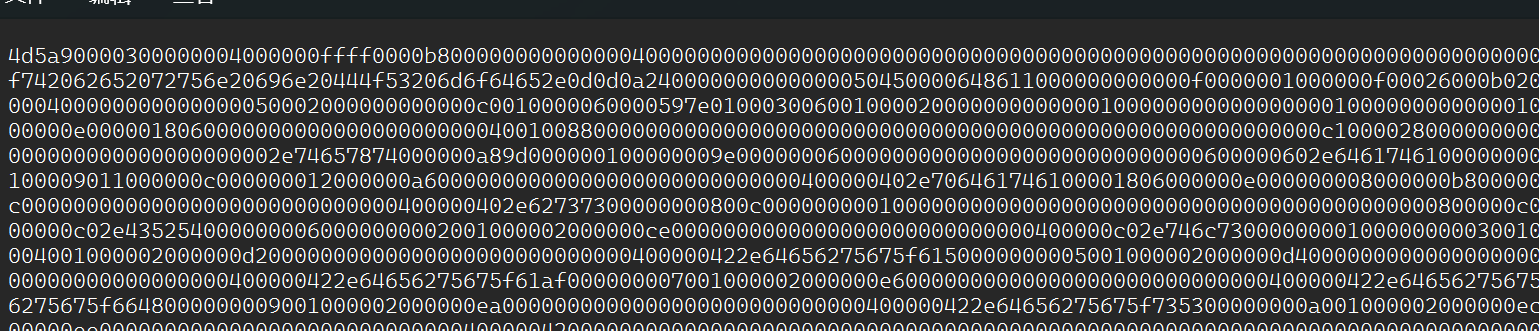
1 | import re |
然后直接ida打开,简单分析了一下:
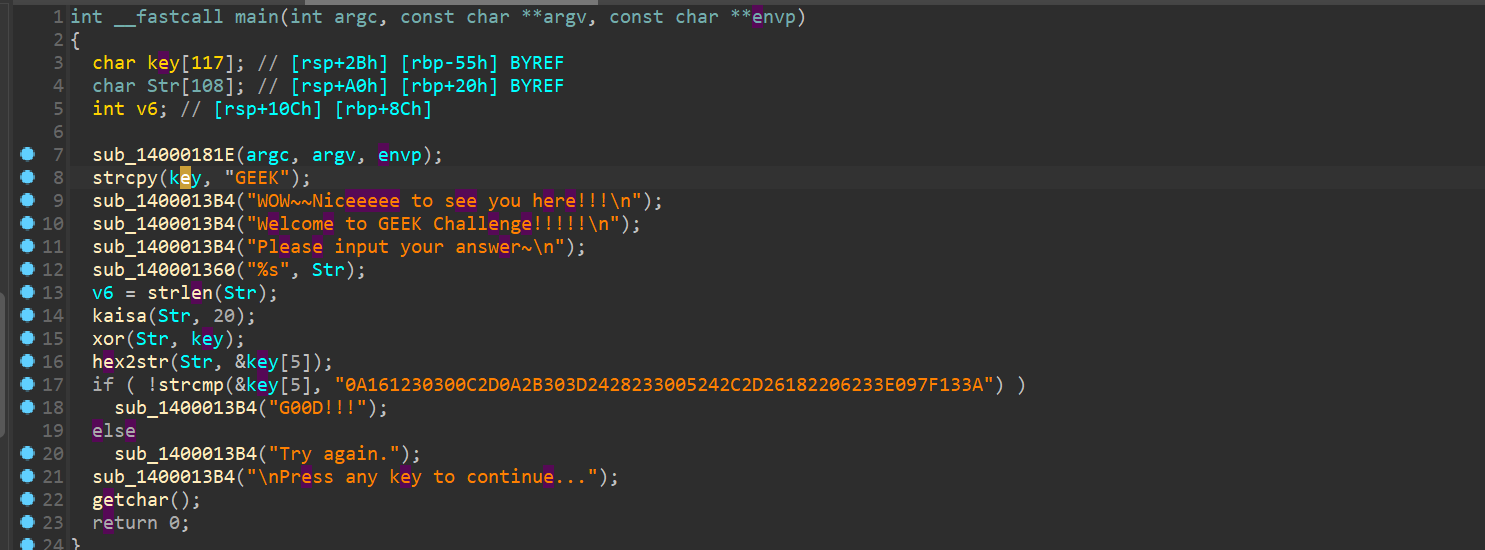
就是先20位的凯撒,然后循环异或key,最后就是hex2str,那么就写个exp先将比较的那一串str转成hex后和key异或,然后再丢到工具当中解密凯撒:
EXP
1 | enc = "0A161230300C2D0A2B303D2428233005242C2D26182206233E097F133A" |

ez_hook
思路
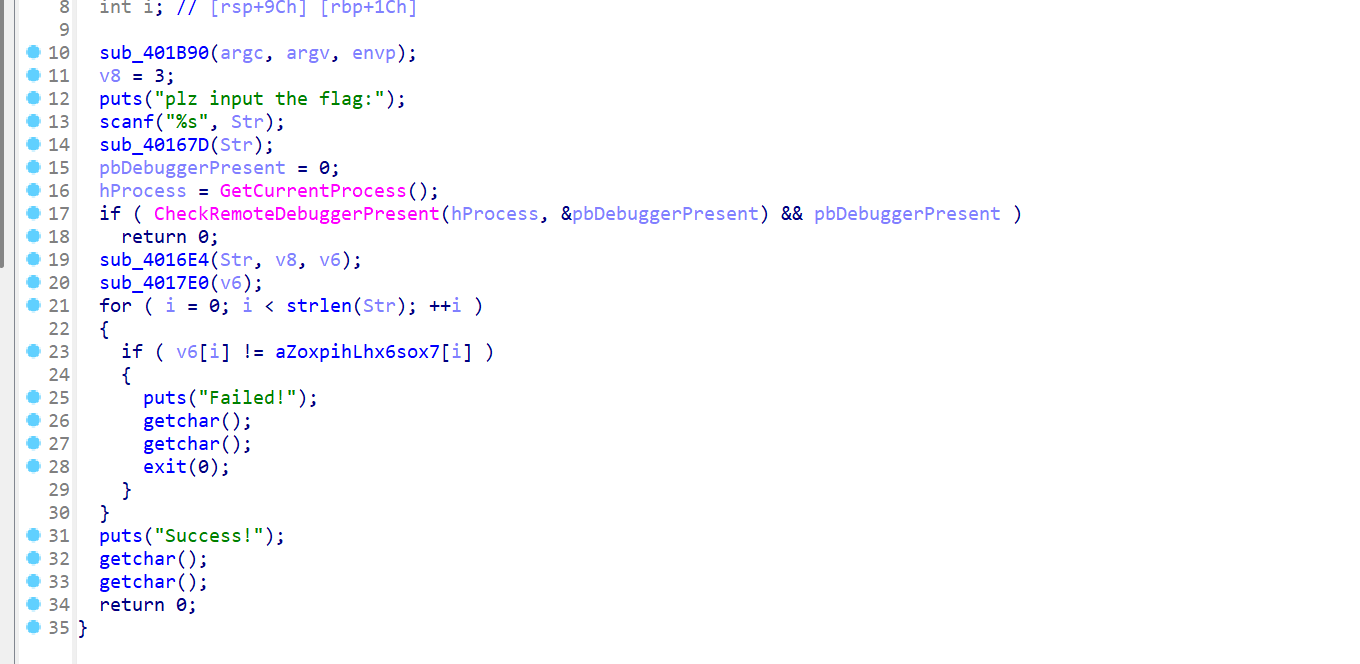
main函数当中的逻辑还是比较简单的,看到sub_40167D, sub_4016E4,sub_4017E0之后再进行比较,密文就是aZo那一串:
zoXpih^lhX6soX7lr~DTHtGpX|长度为26字节,接着从上到下分析这三个函数:
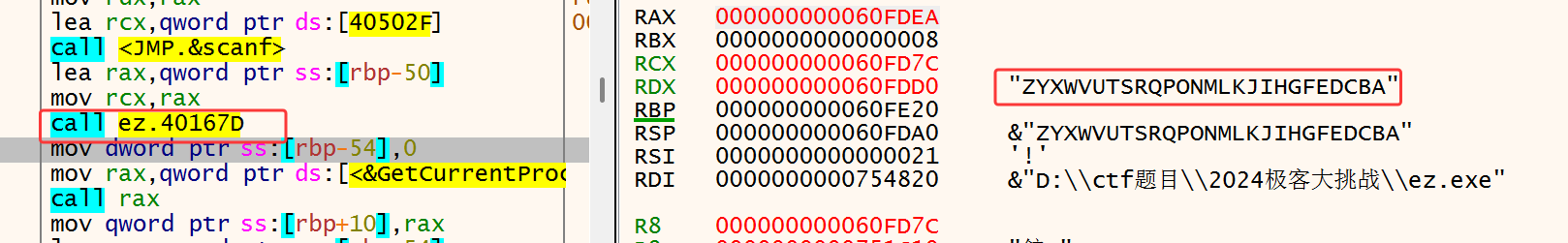
这里直接动调,这里输入ABCDEFGHIJKLMNOPQRSTUVWXYZ 26个字符比较容易观察变化
那么这里第一个sub_40167D就是字符串逆序。接着下一个,这里有反调试还需要绕过一下:
可以看到这里`sub_4016E4(Str, v8, v6);`因为下面的比较也是v6比较,猜测str加密后放到了v6当中,所以v6对应的传参就是`rcx`-->`r8`,步过函数之后就是这样的:
看到就是乱序的混淆,摘出来然后和之前的形成有个map,然后就不用逆向这个算法了
1 | "ZYXWVUTSRQPONMLKJIHGFEDCBA" |
接着用ida分析这个函数:
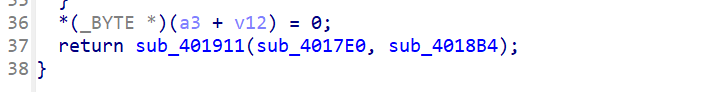
看到最后面return调用的函数传了两个函数指针下去,这个就是一个很经典的hook,将a1函数的首地址指令改成了jmp ...,那么实际上调用的其实是第二个函数
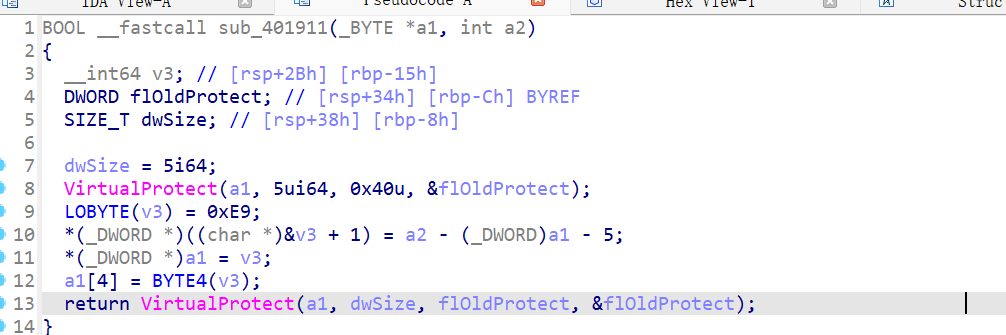
这里看看用来替换的函数是什么:
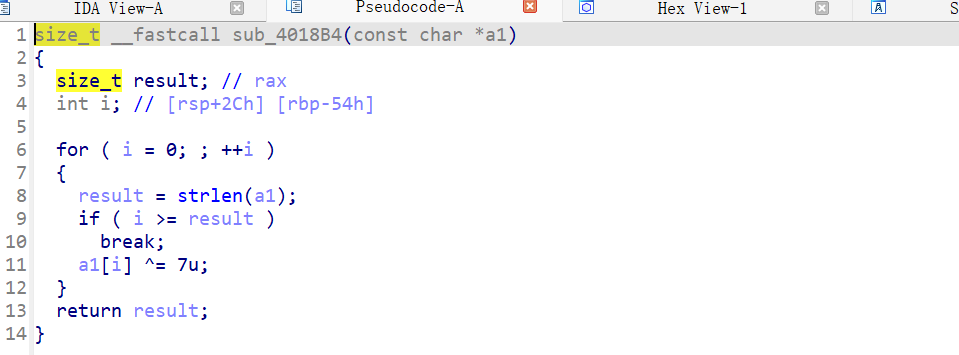
其实就是个异或,那么就能够直接出exp了
EXP
1 | enc3 = list("zoXpih^lhX6soX7lr~DTHtGpX|") |
flag:SYC{you_kn0w_wh@t_1s_hoOk}
ez_re
思路
载入IDA后,main函数中有花指令,先去花
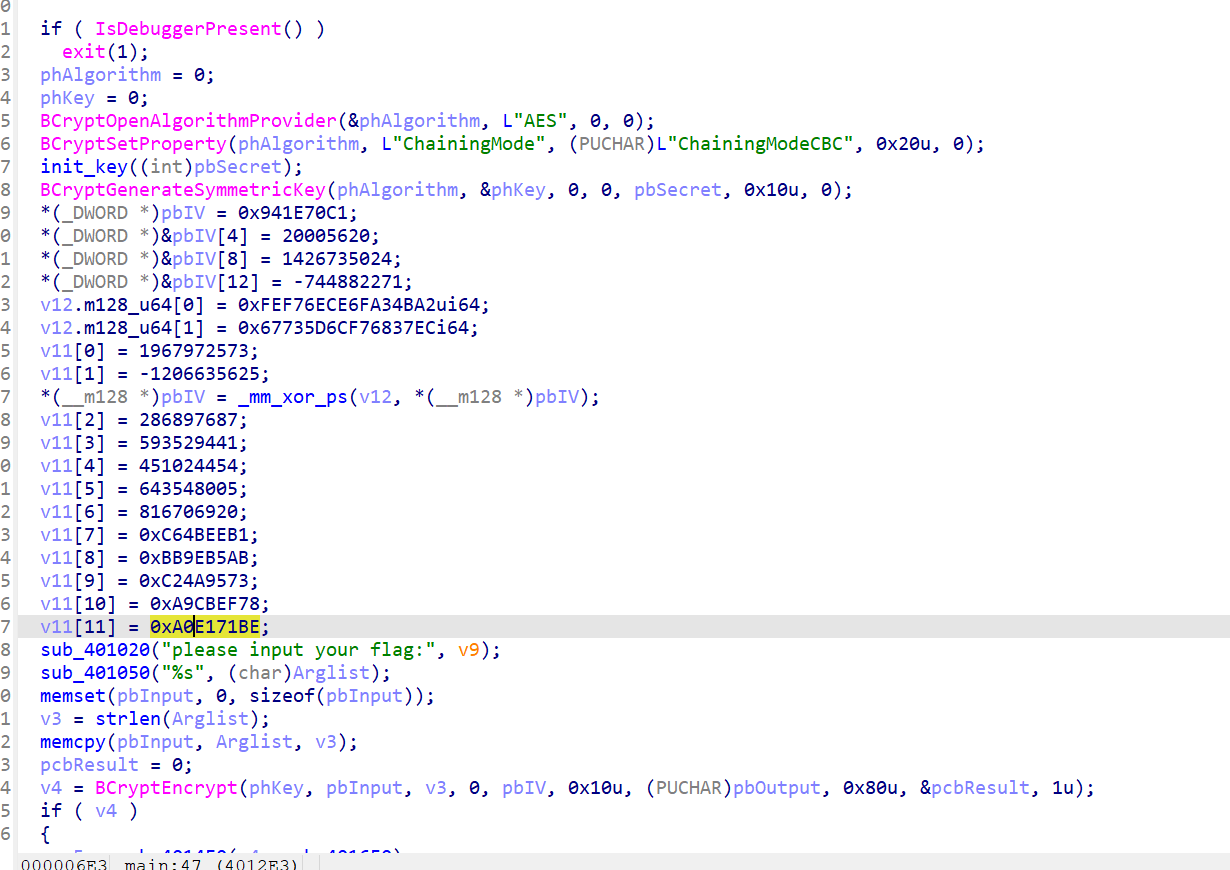
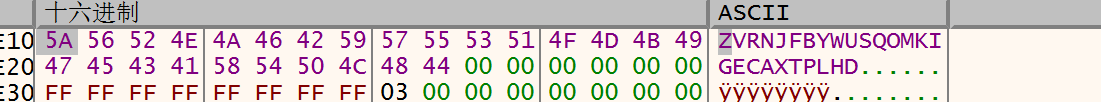
可以看见就是一个AES加密,密钥是动态生成的密钥,还有反调试,那么直接xdbg将密钥调出来:
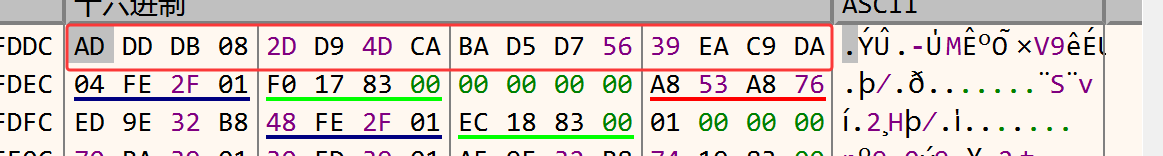
这个就是生成的密钥,然后再将数据提出来就能够结合IDA的数据写exp了
EXP
1 | key = bytes([0xAD, 0xDD, 0xDB, 0x08, 0x2D, 0xD9, 0x4D, 0xCA, 0xBA, 0xD5, 0xD7, 0x56, 0x39, 0xEA, 0xC9, 0xDA]) |
flag:SYC{W0w_Y0U_fOUNdDD_TLS_AND_AeS}
好像是python?
010直接打开下载的附件,是python字节码
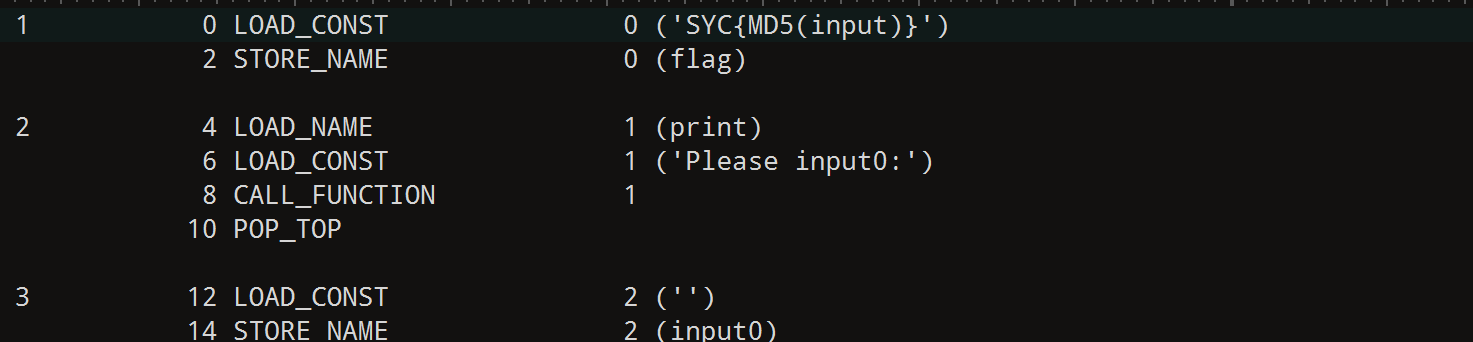
直接ai转成python代码。
1 | flag = 'SYC{MD5(input)}' |
就是个异或加凯撒,直接写解密脚本
1 | import hashlib |
SYC{ed798fdd74e5c382b9c7fcca88500aca}
也许你也听jay
打开附件后就是简单对变量名做了混淆,美化一下,然后就能够写出解密脚本:
1 | xorkey1 = [0x01, 0x02, 0x03, 0x04, 0x05, 0x06, 0x07, 0x08, 0x09, 0x0A, 0x0B, 0x0C, 0x0D, 0x0E, 0x0F, 0x10, 0x11, 0x12, 0x13, 0x14, 0x15, 0x16, 0x17, 0x18, 0x19, 0x1A, 0x1B, 0x1C, 0x1D, 0x1E, 0x1F, 0x20, 0x21, 0x22, 0x23, 0x24, 0x25, 0x26, 0x27, 0x28, 0x29, 0x2A, 0x2B, 0x2C, 0x2D, 0x2E, 0x2F, 0x30, 0x31, 0x32, 0x33, 0x34, 0x35, 0x36, 0x37, 0x38, 0x39, 0x3A, 0x3B, 0x3C, 0x3D, 0x3E, 0x3F, 0x40, 0x41, 0x42, 0x43, 0x44, 0x45, 0x46, 0x47, 0x48, 0x49, 0x4A, 0x4B, 0x4C, 0x4D, 0x4E, 0x4F, 0x50, 0x51, 0x52, 0x53, 0x54, 0x55, 0x56, 0x57, 0x58, 0x59, 0x5A, 0x5B, 0x5C, 0x5D, 0x5E, 0x5F, 0x60, 0x61, 0x62, 0x63, 0x64, 0x65, 0x66, 0x67, 0x68, 0x69, 0x6A, 0x6B, 0x6C, 0x6D, 0x6E, 0x6F, 0x70, 0x71, 0x72, 0x73, 0x74, 0x75, 0x76, 0x77, 0x78, 0x79, 0x7A, 0x7B, 0x7C, 0x7D, 0x7E, 0x7F, 0x80, 0x81, 0x82, 0x83, 0x84, 0x85, 0x86, 0x87, 0x88, 0x89, 0x8A, 0x8B, 0x8C, 0x8D] |
解出来是一个网址https://am1re-sudo.github.io/Coisni.github.io/
在里面获取到了两个东西:Q7u+cyiOQtKHRMqZNzPpApgmTL4j+TE=,key:lovebeforeBC还有RC4,那么直接厨子一把梭:
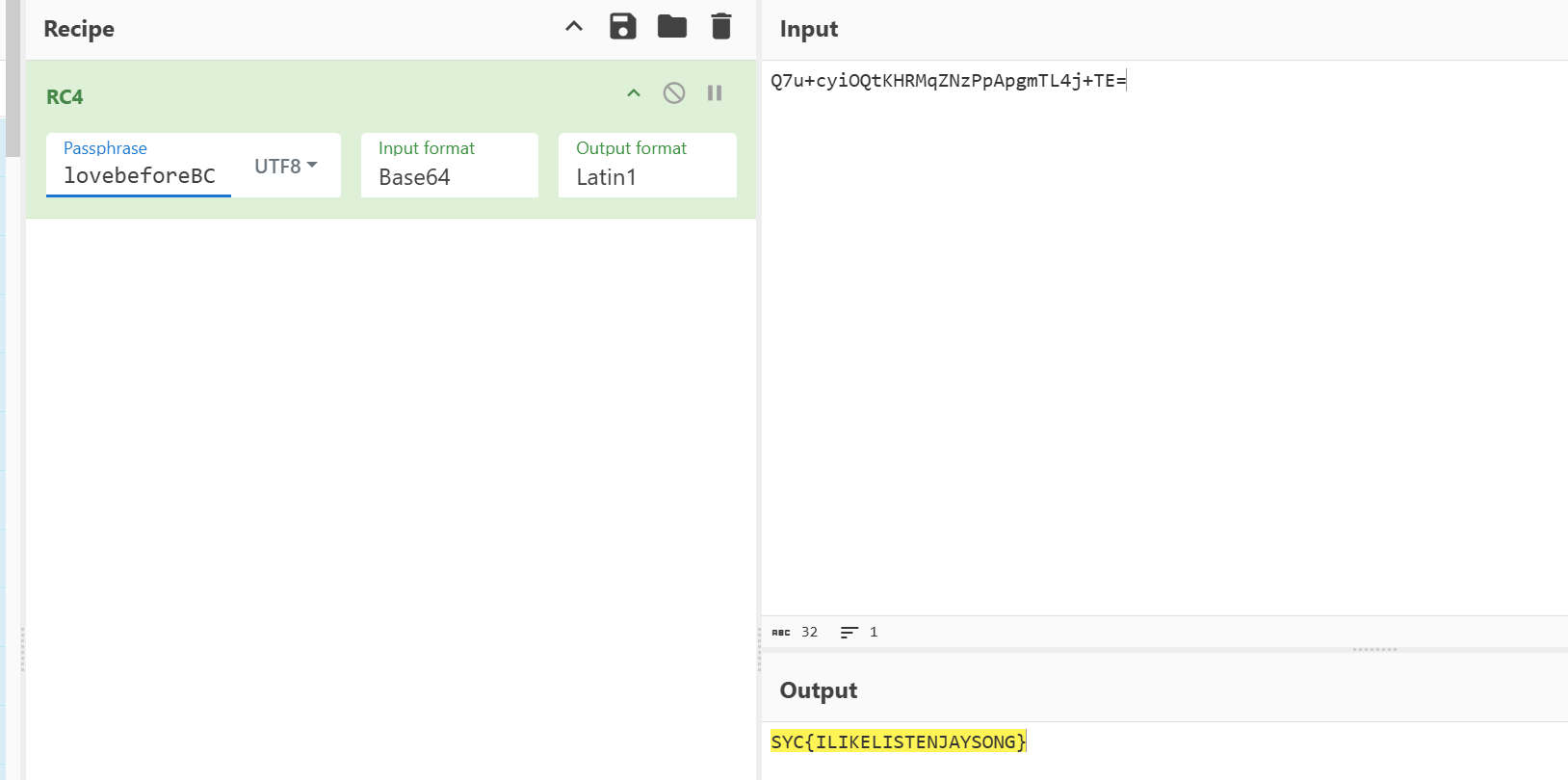
SYC{ILIKELISTENJAYSONG}
baby_vm
思路
载入ida后分析一下vm的逻辑,看到有一个比较抽象的运算:
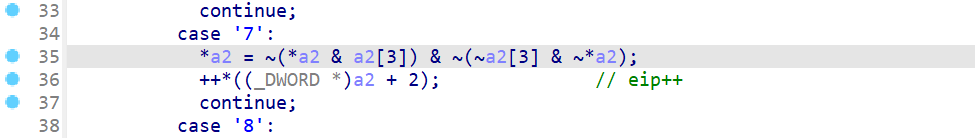
就是这一块,可以简化成~(a0 & a3) & ~(~a3 & ~a0),然后辗转了解了一下,可以用德摩根律直接化简,最后就等价于a0^a3,然后将代码逻辑抄出来,然后硬看吧:
1 | opcode = open("baby_vm.exe","rb").read()[0x5840:0x5840+0xf0] |
生成出来的逻辑分析了一下,因为没有其他参数的限制,所以只执行了一轮,然后一轮当中有0,1下标分别对应两种加密方法,又因为是逐字节加密,可以直接使用爆破:
1 | flag = [] |
SYC{VM_r3verse_I0Oks_llke_yON_@r3_pr37ty_skiLl3d!}
拓展
之前看过有位师傅的wp,vm还能够用z3直接跑出来,此处转载文章:https://blog.hxzzz.asia/archives/103/
贝斯!贝斯!
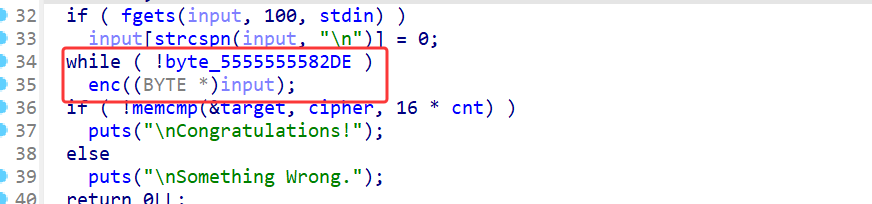
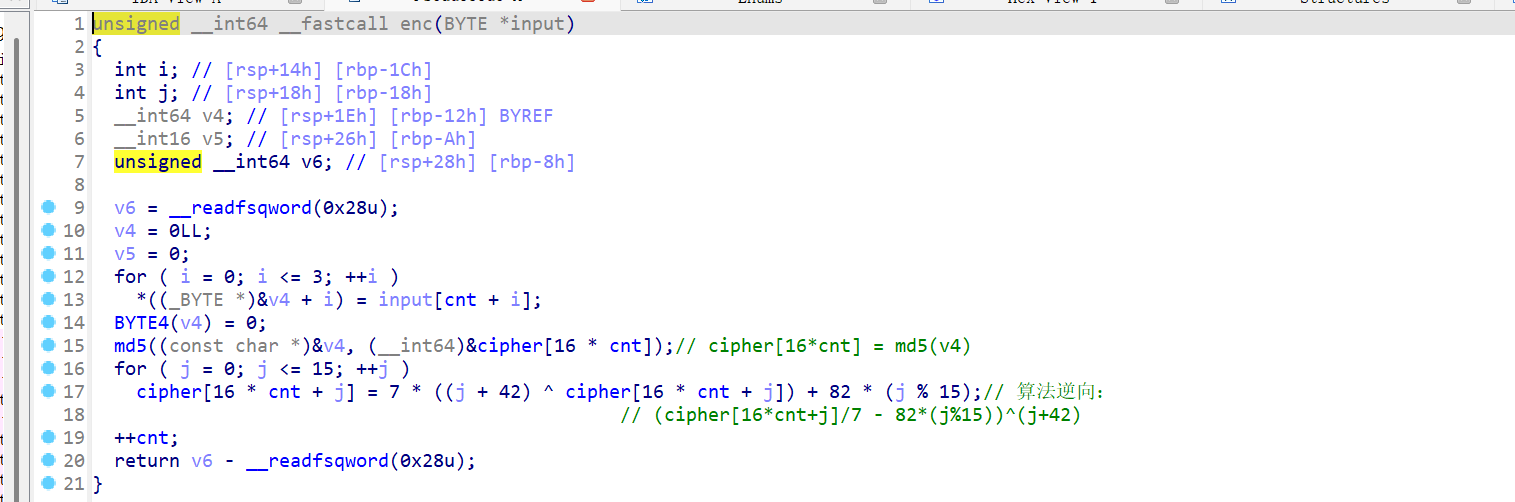
IDA载入发现有不少加密函数,但是真正做加密的只有两个函数,只使用了base58和base85的加密
但是base58和base85都进行了换表的处理,base58是通过时间戳:整天数来进行随机排序base58的表,而base85的表是通过RC4的密钥流来进行乱序,这个可以直接动调拿出来
密文:RjB6Myu#,>Bgoq&u.H(nBgdIaOKJbgEYj1GR4S.w
先将base85的表抓出来解密:eM+wr=x8aYZ/[zU$yRB&kbO;%p0P5f*7d(n]1Eug4ojc62AC,v39!h-^qQ.G?s)i:DFlS<>#@HINJTmtKLVWX
然后就是base58了,这里由于使用了时间戳的方式进行对码表的打乱顺序,所以需要进行爆破,生成所有的码表:
1 |
|
然后就能够用生成的编码表集进行解密了:
1 | b58_table = "eM+wr=x8aYZ/[zU$yRB&kbO;%p0P5f*7d(n]1Eug4ojc62AC,v39!h-^qQ.G?s)i:DFlS<>#@HINJTmtKLVWX" |
SYC{th1s_ls_an_ez_base}
blasting_master
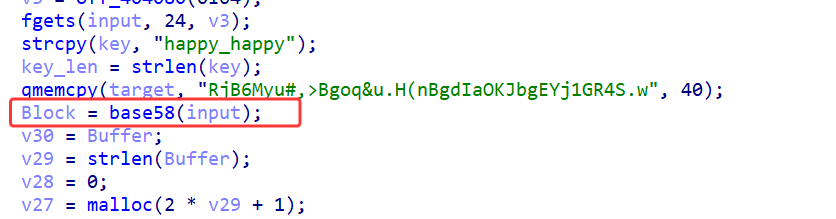
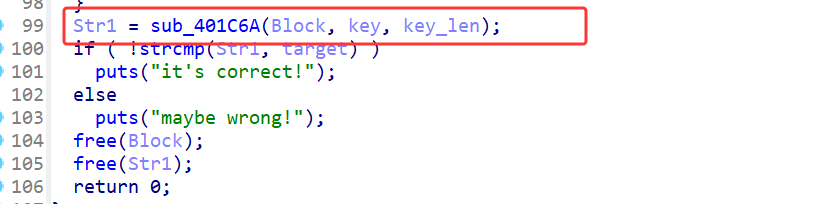
ida打开就能看到main函数很明显的逻辑了:
大致就是循环做加密,然后比较字符串。看看加密的逻辑
将input的四个字符拼接成字符串,然后做md5加密,加密后对md5的每个字节的值单独做一次加密,这里需要注意的是:
这里的字符拼接是4个4个拼接,拼接完一次后指针只后移一位,所以相当于每四次md5加密有3次是没用的,其次就是对md5加密结果的加密,这里
*7的解密需要用到有限域下的逆元,然后就能够写出解密脚本了,最后的还需要将第40个md5爆破一下:
1 | from Crypto.Util.number import * |
flag:SYC{W0w!y0u_@re_th3_BeSt_blasting_Exp3rt!!}
你干嘛~~
32位程序,ida打开之后发现main函数不全,估计是有花指令,往下拉看看情况
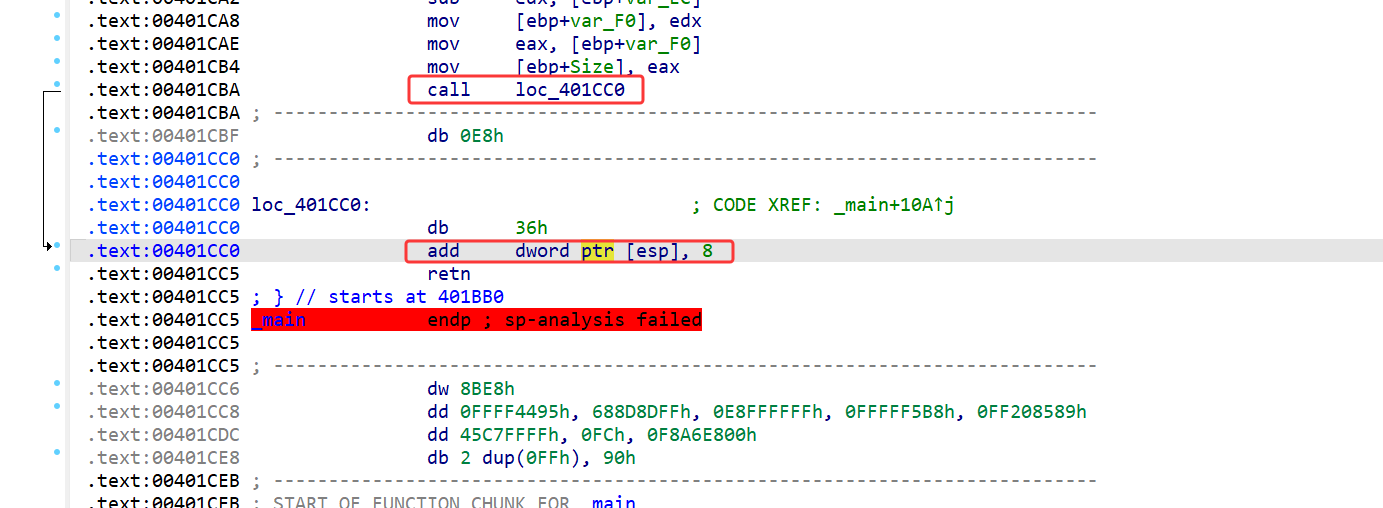
一开始直接将这个改成了,jmp 0x401cc7,能够正常反编译,但是发现好像很不对劲
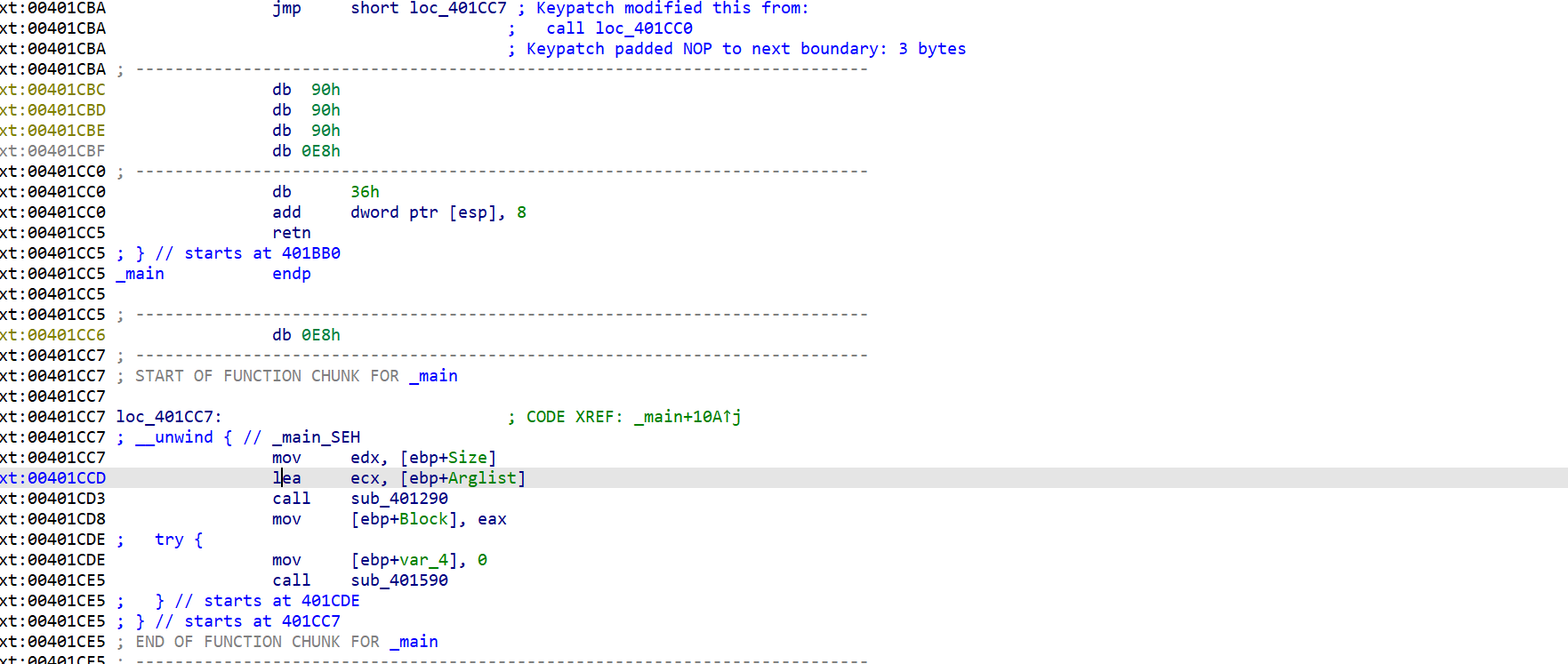
主要是下面还有一部分不能够正常反编译,而且这里会直接调用CxxThrowException然后调试的时候整个程序会崩掉,而且因为这个seh,导致下面的部分无法正常反编译,猜测是在SEH当中做了反调试。那么直接将这一段给nop掉,然后main函数就能够正常反编译了:
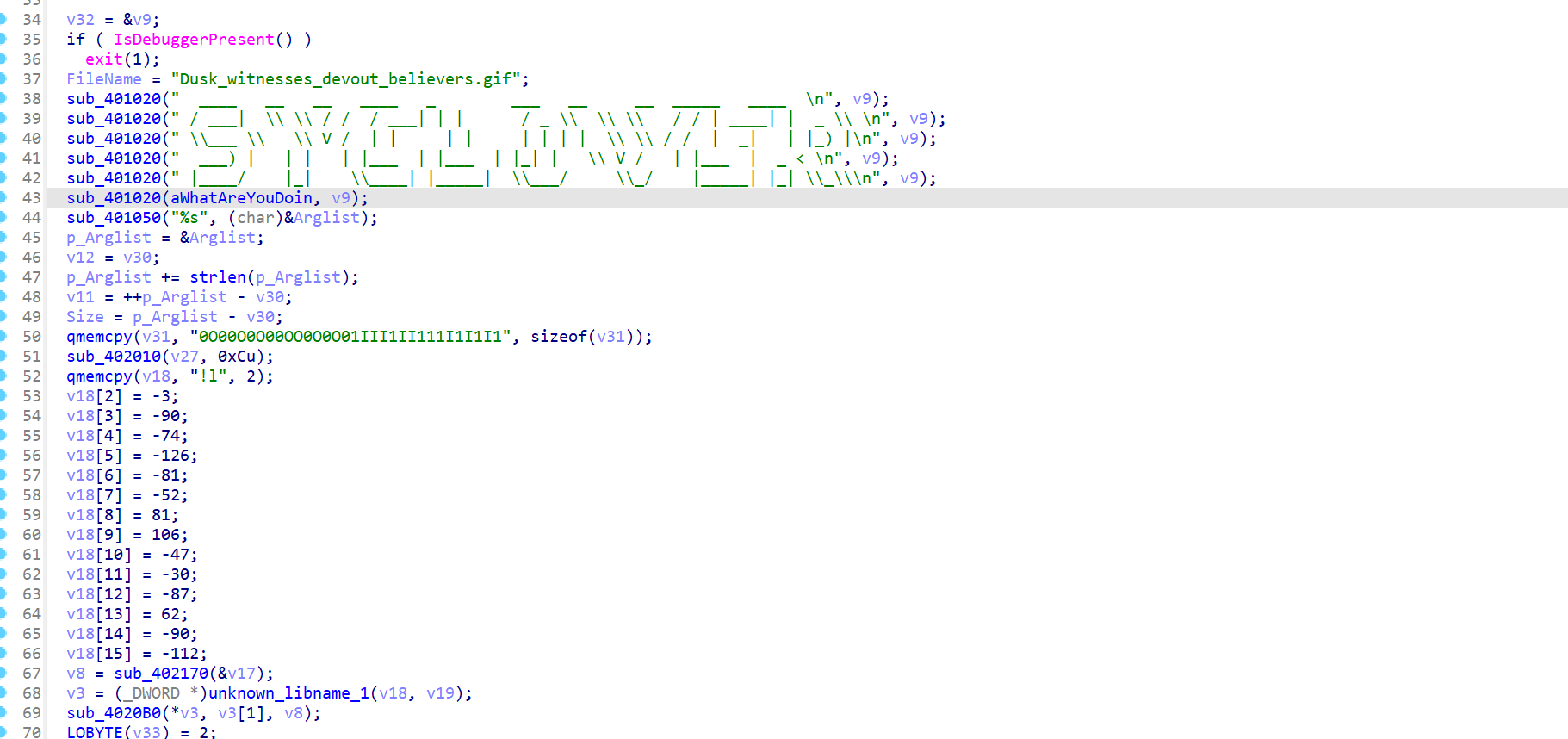
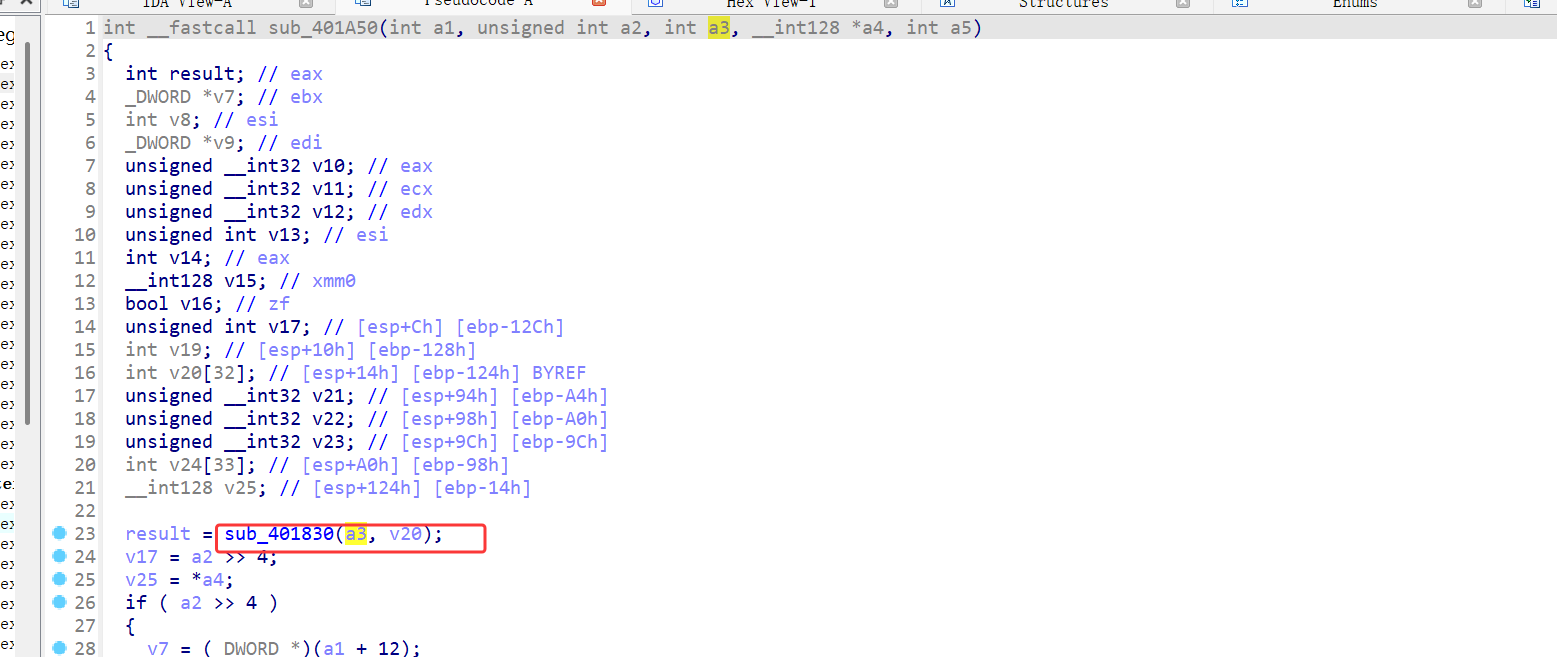
整体逻辑看了一下,如果输入正确会直接把另一个文件用我们的输入当成key进行异或的解密。但是中间一部分感觉比较恶心,做了不少的指针转换,核心部分就是:
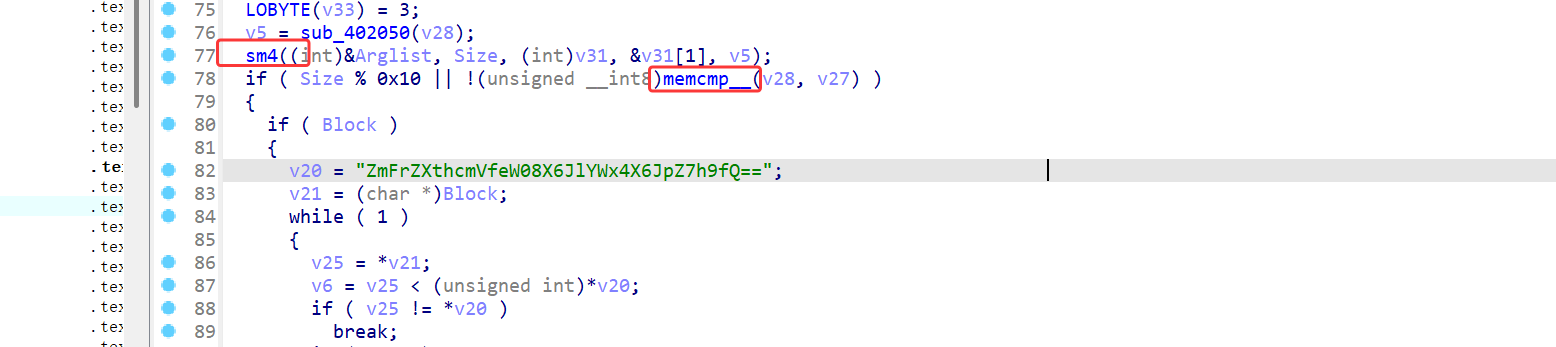
经过调试发现,上面不少函数其实只是干扰,主要就是sm4这个加密,和下面这个比较函数(虽然不知道这个是怎么实现的),而target的值就是上面v18整个数组。
而这里的sm4,传入的v31,&v31[1]其实是sm4的key和IV,在函数内部发现a3也就是v31->0O00...就是加密的key,那么直接用厨子解一下:
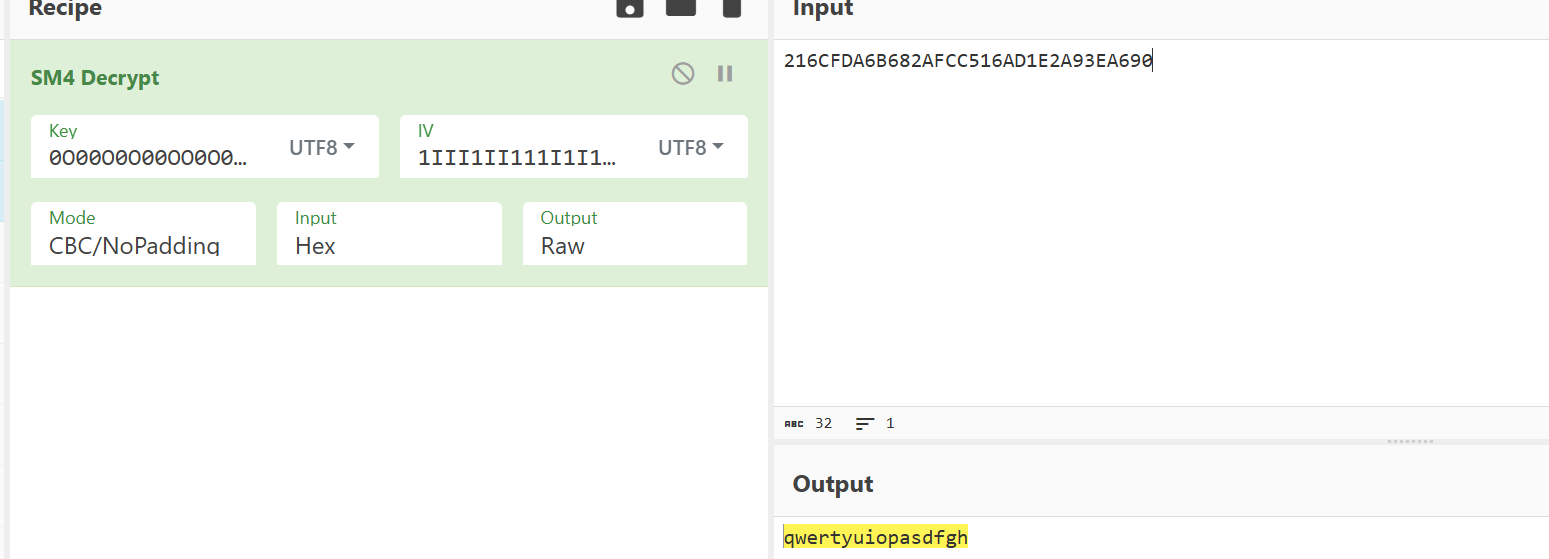
正确输入:qwertyuiopasdfgh
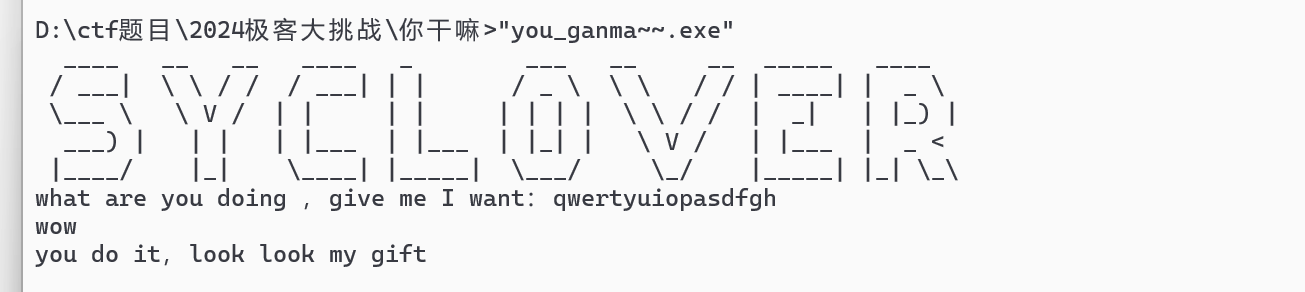
然后就会发现多了一张gif图,里面就有flag:
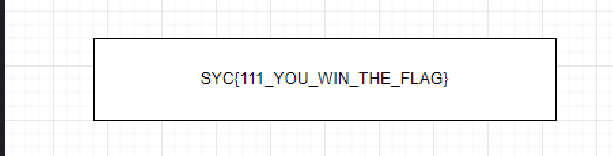
SYC[111_YOU_WIN_THE_FLAG]
giraffe_eat_rainbow
这题是一个简单的ollvm的控制流平坦化,可以直接使用angr跑出来:
1 | import angr |
flag:SYC{yOU_girAFe_L0Ve_EaT_W0bN1aR
